
Tracking an Anonymous Peer Using WebRTC
It's was about a year ago, someone in my rather big office (100~200 people) started to send annoying emails with cheesy phrases and images regarding the new…

It's was about a year ago, someone in my rather big office (100~200 people) started to send annoying emails with cheesy phrases and images regarding the new…

Exactly 2 months ago The 6th Annual International Cybersecurity Conference was held in Tel-Aviv. It was packed with presentations from leading security…
tl;dr; Browsers doesn’t handle webcam permissions well enough. Users should be extremely wary about what’s going on in their browser. From a list of 30 bugs…
tl;dr; The concept of session memory is not valid anymore in today’s browsers. Even sessionStorage is not cleared after closing the tab. It’s easily revived…
tl;dr; I’ve created mechanism that will leverage the secure nature of the browser sessionStorage or memoryStorage for authentication and will still allow the…
tl;dr; I found a bug in Google Chrome that allows an attacker to listen on the user speech without any consent from the user and without any indication. Even…
tl;dr I stumbled upon some CSRF flaws in a very popular e-commerce website. CSRF flaws are generally overlooked and the only way for you as the user to…
After seeing in the previous post how Data-URIs can be used as a mechanism to easily carry malicious code, I’ll elaborate more about the issues it presents.…
What an awesome format is SVG, so powerful and so well supported by browsers. And yet it is barely being used, it’s not getting the love it deserves. Well,…
iPhone 1. Don’t jailbreak, a not jailbroken iPhone is a pretty secure device. 2. Use PIN code Settings -> General -> Passcode (and not something like 1234) 3.…
Three weeks ago Path.com was fined for stupidly stealing their user’s contact list and saving it onto their servers. Path’s doing was obviously wrong but I’m…
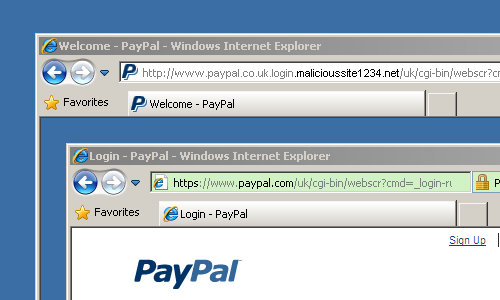
So my favorite script kiddy and copycat, Feross (copied, note the shameless “I discovered” in his Quora post, LoL) Found a social engineering flaw in the HTML5…
Two weeks ago this guy managed to revive my 3 years old Webcam ClickJacking POC and also managed to revive some of the buzz surrounding it. The revived attack…
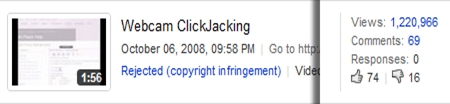
Update: Youtube has revived my video. you can now watch Webcam Clickjacking as much as you like. — Remember ClickJacking? The generic flaw in web browsers and…
I was going to congrat Adobe for their fix to the private browsing in Flash, this was my original text: I’m glad to say that Adobe has fixed the minor issue…
To know if the user is currently in normal or private browsing mode can be valuable info for any ads providers and spammers, but not only. With the upcoming…
I was checking my email when all of a sudden I saw this email “New WordPress Blog”. I didn’t remembered adding, updating or doing anything with my blog. I…
Adrian Parr, a Flex blogger mostly known for his post listing of AS3 frameworks got hacked by some political lamers. The whole blog is replaced with common and…
Two days ago, the first Israeli Google Developer Day was held. It was a colorful and interesting event, to the best of google tradition. Yesterday, all…
Update: Adobe has fixed this issue by framebusting the Settings Manager pages. Now, 99.9% of the users are protected from this specific exploit. Congrats on…
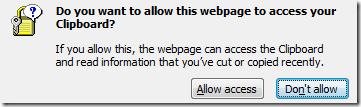
Recently, a questionable Flash feature of writing to the user’s clipboard has been exploited. Adobe will finally fix this feature and it’ll require user…
Update: Added a sterilized demo and the source code. CSRF (Cross Site Request Forgery) is considered one of the most widely spread exploits in websites today.…
Update: I’ve posted a real world example of this bug being exploited. This one has the same behavior on IE6, IE7 and IE8 betas. I have only tested this with…

Update: You need to check the website to see what I’m talking about The police (not the band) in general is a problematic institute. Giving average (and below)…
Update: Adobe Product Security Incident Response Team (PSIRT) has referred to this “Clipboard attack” Update 2: Aviv Raff has updated me about the fact that it…
The first part of an hacker’s job would be to gather some information about her target, server, technology and software that runs on the desired target. With…
Update:Apparently SP3 doesn’t downgrade the player. It’ll only install an older version 9.0.115 if you don’t have the latest 9.0.124 already installed,…
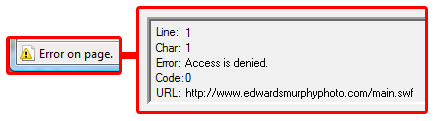
FLA is one of these file format that we’re used to freely open without any fear. Our complete confidence is going to change since a new exploit has been found.…
Apparently Adobe has fixed the bug I’ve found that enables a swf file to crash the browser, with the last version of the Flash Player (9,0,115,0). I don’t know…
I’ve just came across of a way to kill the Flash player with a few lines of AS 2.0. I know of at least one other way of killing the Flash player along with…
Valve, the maker of two of the best games of all time, Half-Life 2 and 1, was already hacked once in 2003. The source code of it’s highly anticipated and…